How Tech-Driven Businesses Can Prioritize Application and Cloud Security
Technology companies face a relentless onslaught of cyber threats. Breaches and data leaks are no longer a question of “if” but “when.” For MSMEs, startups, and established tech giants alike, a robust cybersecurity posture is not just a luxury but a necessity.
Recent high-profile attacks have underscored the importance of focusing on two critical areas: application and cloud security. Applications are the gateway to sensitive data, and the cloud has become the backbone of modern business infrastructure.
However, these technologies also present unique vulnerabilities that can be exploited by malicious actors.
Sec1.io is at the forefront of this cybersecurity paradigm shift. Recognizing that traditional security measures are no longer sufficient, it offers a comprehensive suite of services tailored to the specific needs of tech-driven businesses.
“The approach needs to be proactive, not reactive. It is best to focus on building resilience into your digital infrastructure right from the get-go.” – Lorna Bondoc
Related Stories:
- Jollibee data breach. Jollibee is currently investigating a reported data breach in its delivery system, which may have affected millions of customers. The National Privacy Commission (NPC) is also looking into the matter.
- PhilHealth ransomware attack. In September 2023, the Philippine Health Insurance Corporation (PhilHealth) suffered a ransomware attack, leading to the exposure of personal data, including hospital bills, internal memos, and identification documents.
Application Security
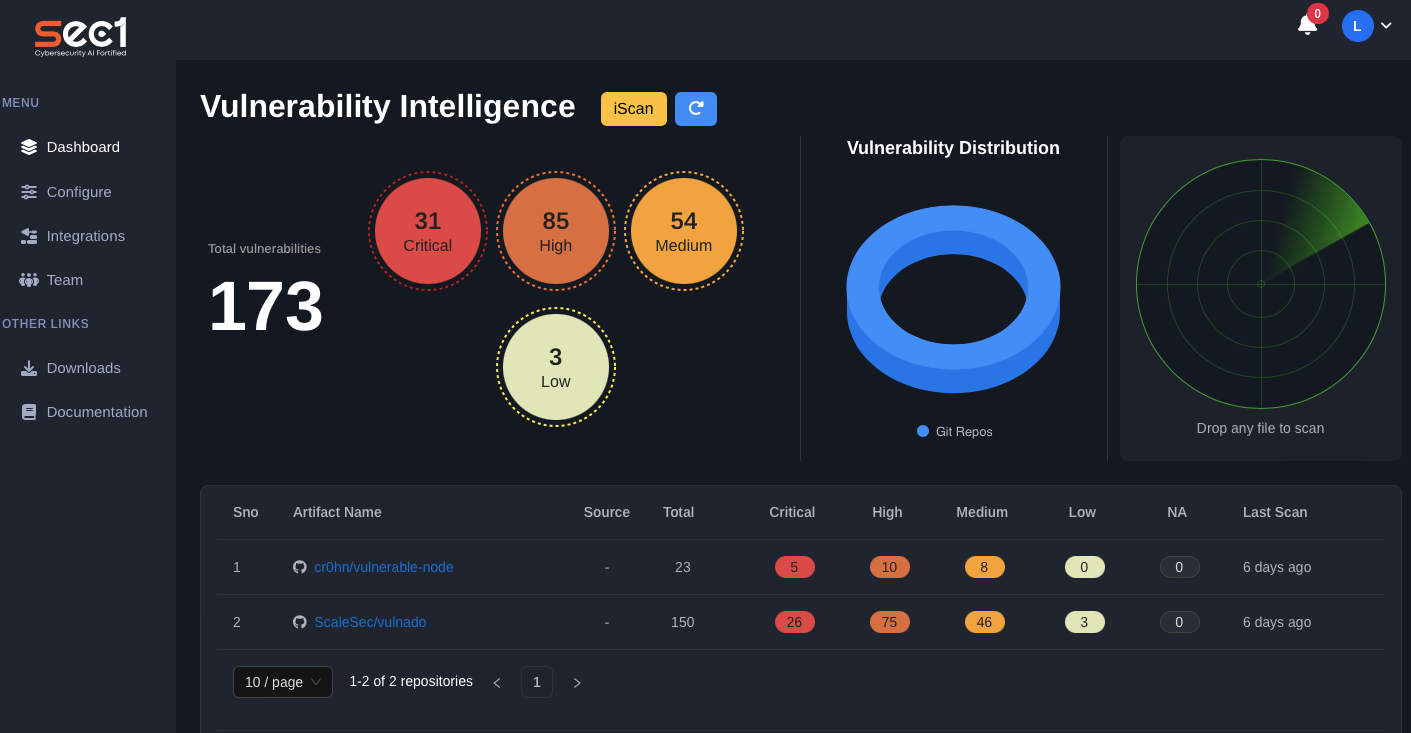
Applications are often the weakest link in a company’s security chain. Sec1.io’s application security services include:
- Secure Code Review. Identifying and mitigating vulnerabilities in your source code before they are exploited.
- Penetration Testing. Simulating real-world attacks to uncover weaknesses in your applications.
- Vulnerability Assessment. Regularly scanning your applications for known vulnerabilities and providing remediation guidance.
- Security Training for Developers. Equipping your development team with the knowledge and tools to build secure applications from the ground up.

Cloud Security
As businesses increasingly migrate to the cloud, it’s imperative to ensure that your data and infrastructure are protected. Sec1.io’s cloud security experts can help you:
- Understand the Shared Responsibility Model. Demystifying the division of security responsibilities between you and your cloud provider.
- Implement Strong IAM Controls. Ensuring that only authorized users have access to your cloud resources.
- Protect Data in the Cloud. Encrypting sensitive data and implementing additional security measures.
- Continuously Monitor Cloud Environments. Detecting and responding to potential threats in real time.
A Complete Approach to Cybersecurity
While application and cloud security are paramount, Sec1.io takes a holistic approach to cybersecurity. It offers a range of additional services, including risk assessments, incident response, compliance management, and security awareness training.
Partnering with YOVEO
Sec1.io’s partnership with YOVEO ensures that your business not only remains secure but also thrives in the digital space. YOVEO’s expertise in web design and development, SEO, social media marketing, and content creation can help you amplify your online presence and drive business growth.
Sec1.io and YOVEO are committed to helping you navigate online and achieve your business goals. Prioritize application and cloud security, and partner with experts who understand the unique challenges of tech-driven businesses.






